n the United States, ~25,000 women become pregnant through rape each year. In 27 states there are no laws which protect the custodial rights guaranteed to the mother of the resulting child. ... Read More
The murders which occurred at Sandy Hook Elementary School in Newtown, CT. shocked the community, the state and the country. Resources are flowing in and we have heard of the acts of heroism displayed by the deceased adults and many others. The sadness of... Read More
This morning, I, like so many others across the globe, sit with tears streaming down my face and into my lap as I think about the 26 souls who are now in Heaven on a direct path from the Sandy... Read More
As we roll into this holiday season please take a moment and think about the children who are orphans and/or foster children. These children are in a state of flux. Those of us who haven’t experienced being a child in... Read More
I recently viewed an wonderful infographic full of not-so-wonderful data: “Equal Education, Unequal Pay” from the good folks at "Learnstuff." This infographic depicts numerous data points which highlight, regrettably, the disparity between men and women wages. The real... Read More
On Friday, 30 November 2012, two miscreants (Terrence Williams and Charles Deville Nash) were sentenced to extended stays within the federal prison system for trafficking young women within Western Washington, and to/from other states. The pimps would advertise the... Read More
This weekend, one of the charitable groups which I actively and financially support, Northwest Harvest, teamed with King5 TV in a "Home Team Harvest" campaign to raise through donations of both food and money to provide for 3 million meals... Read More
Liberty County prosecutors described Jared Len Cruse as one of a "pack of dogs" who gang-raped an 11-year-old Cleveland girl, while the defense likened the girl to a "spider" who lured men into her web.... Read More
On this Black Friday, the Friday where we have 1 in 6 food-insecure, let us get our collective acts together and spend some of that Retail Therapy energy on hunger in America.... Read More
Yesterday my stomach turned. I read this headline: "Moraga School District: Child sex abuse victim was 'careless and negligent' The child being discussed was 12 years old. From under what rock did this school district... Read More
This morning I woke up circa 3 AM courtesy of Dewey, one of the warmest, gentlest and loving dogs.,...who went back to sleep. I on the other hand, did what I do every morning at this time, I read,... Read More
On the 18th of October, the Mayo Clinic Center for Social Media announced the publication of “Bringing the Social Media #Revolution to Health Care” (Mayo Clinic) – for those involved in the health care vertical and with social media responsibilities... Read More
The stalker, may he burn in hell, a male predator on-line convinced a 12-yr-old Amanda whom he befriended in a chat room to flash her breasts over an internet connect and did a screen grab of the event. For... Read More
The suicide death of 15 year-old Amanda Todd was a preventable and tragic event. Her mother, Carol Todd, has asked that her daughter's death be used as a means to prevent the death of another child. Our children... Read More
Today is the day of the girl - October 11, 2012. Education is the key to moving the millions out of abject poverty. Today, there are 250 million girls in poverty asking for an education. Learn more...... Read More
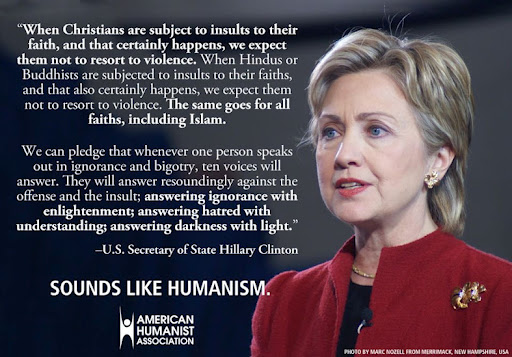
Freedom is seldom free - served to remind all of us why we were serving our nation abroad. It also served to remind us that our freedoms, such as religious freedom and freedom of speech, are not universally enjoyed.... Read More
Labor Day is celebrated in honor of each and every one of us - the workers. It is an inclusive celebration. A remembrance of the efforts and success in bringing to our existence acceptable wages, fair and suitable... Read More
Of the 925 million in this world who live with food insecurity every day, 528 million of them live in the Asia and Pacific regions. Think about that number it is over 50% of those who deal with hunger... Read More
I recently read a piece put out byUpali Wickramasinghe, the Regional Advisor on Poverty Reduction and Food Security (CAPSA-ESCAP) in which it was articulated of the 925 million in this world who live with food insecurity every day, 528 million... Read More
Kameron Jacobsen - Age 14, four months into his Freshman-year of high school, Kameron took his own life in January 2011. According to his parents, he had been the target of bullying both at Monroe Woodbury High School and... Read More